Executive Summary
Enterprises of all types are becoming more vulnerable to cyber threats due to their increasing reliance on computers, networks, programs and applications, social media, and data. Security breaches can negatively impact organizations and their customers, both financially and in terms of reputation. Global connectivity and availability to information by users outside the organization expand risk beyond what has been historically addressed by IT general and application controls. Organizations’ dependencies on information systems and the development of new technologies supply traditional evaluations of IT general and application controls inadequate to provide assurance over cyber security.
What is cyber security?
Cyber security refers to the technologies, processes, and practices designed to protect an organization’s information assets – computers, networks, programs, and data – from unauthorized access. With the frequency and severity of cyberattacks on the rise, there is a significant need for improved cybersecurity risk management.
Key Risks and Threats Related to Cyber security
Cybersecurity is relevant to the systems that support an organization’s objectives related to the effectiveness and efficiency of operations, reliability of internal and external reporting, and compliance with applicable laws and regulations. An organization typically designs and implements cybersecurity controls across the entity to protect the integrity, confidentiality, and availability of information. This is ‘what is cyber security all about’.
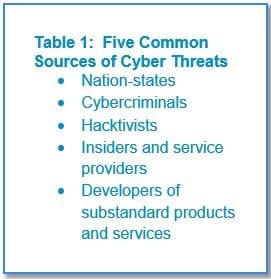
Cyberattacks are perpetuated for varied reasons including, but not limited to: financial fraud, information theft or misuse, activist causes, to render computer systems inoperable, and to disrupt critical infrastructure and vital services of a government or organization. Five common sources of cyber threats are listed in Table 1.
To understand the cyber threats relevant to an organization, it is important to determine what information would be valuable to outsiders or cause significant disruption if unavailable or corrupt. Also, it is important to identify what information may cause financial or competitive loss or reputation damage to the organization if it were acquired by others or made public. Examples of information to consider include: customer and employee data, intellectual property, supply chain, product quality and safety, contract terms and pricing, strategic planning, and financial data
The industry in which the firm operates set up an important context when recognizing cyber threats. For example, retailers may focus on protecting customer data and ensuring that customer services are not disrupted. Intellectual property may be a key concern for organizations centered on research and development. Manufacturers may concentrate on the reliability and efficiency of production and supply chain systems, as well as the quality and safety of products. Professional services firms may be most concerned with sensitive commercial information contained in contracts and financial costing models.
Procedure for Assessing Cyber security Risks
The six correlated elements of the framework mentioned below can be used to access the design and operating effectiveness of management’s cybersecurity controls and governance.
1. Cyber security Governance
Strong cybersecurity governance depends on:
– Cooperating and assembling cybersecurity risk intelligence and expertise based on threats that could affect the organization
– Setting risk appetite and tolerance.
– Planning for business continuity and disaster recovery in the event of an interruption.
– Responding promptly to security breaches.
– Establishing a culture of awareness of cybersecurity risks and threats.
2. Inventory of Information Assets
When evaluating the organization’s information assets, the following should be considered:
Data
– Types (like transaction, IT configuration, unstructured)
– Classification (enables standardization and prioritization)
– Environments (like data warehouses, key data bases)
Infrastructure repository of technology assets
– Servers
– Network devices
– Storage
– End-user devices
External relationships
– Third-party hosted environments
– Sharing of data files with external organizations (like vendors, regulatory bodies, governments).
3. Security Configurations
Centralized, automated configuration management software can be used to establish and maintain baselines for devices, operating systems, and application software. Using management software is more effective than managing systems manually or in a nonstandard fashion. Information security and the audit activity should review baselines to ensure an accurate assessment of environments based on risk can be achieved (for example externally facing web environments may require additional protection). Processes to apply important spots, as well as software and hardware updates, are also needed to ensure secure configurations remain current as new threat information becomes available in the industry.
4. Access Management
Management should consider implementing preventive controls such as having a process to approve and grant access to users based on job roles. Additionally, a process to detect when employees move within the organization would help to ensure that user access is adjusted and relevant to the new role. The audit activity may perform a review of user access to key data and systems to validate that access levels are justified for the current roles.
5. Prompt Response and Remediation
The capability of the organization to promptly communicate and remediate risks indicates the program’s effectiveness and level of maturity. Mature programs are able to continuously shorten the time to management response. One role of the second line of defense is to:
– Communicate risks that matter.
– Enact remediation.
– Track identified issues to resolution.
– Inclination and direction on resolution across the entity.
6. Ongoing Monitoring
As a final component of this framework, continuous auditing of each of the five components described above when conducted will help to determine how risk is managed and how well corrective action is operating. An effective assessment approach requires more than routine, checklist adherence surveys. The second line of defense is expected to implement a monitoring strategy designed to generate behavioral change that includes:
– Access-level assessment and scanning that involves observing people with access to sensitive information to measure related cybersecurity risk.
– Vulnerability assessment.
– Third-party risk assessments and monitoring.
– Penetration testing.
– Malware.
– Incident monitoring and response.


I Fashion Styles
wonderful publish, very informative. I ponder why the other experts of this sector don’t realize this. You should proceed with your writing. I am sure, you have a great readers’ base already!
wings io
This piece of writing is actually a nice one it
assists new net visitors, who are wishing for blogging.
Don
I every time spent my half an hour to read this web site’s articles daily along with a mug of coffee.